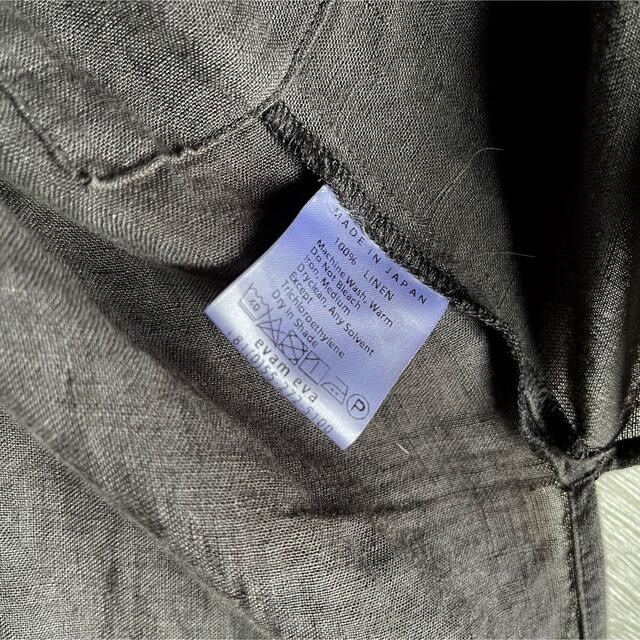
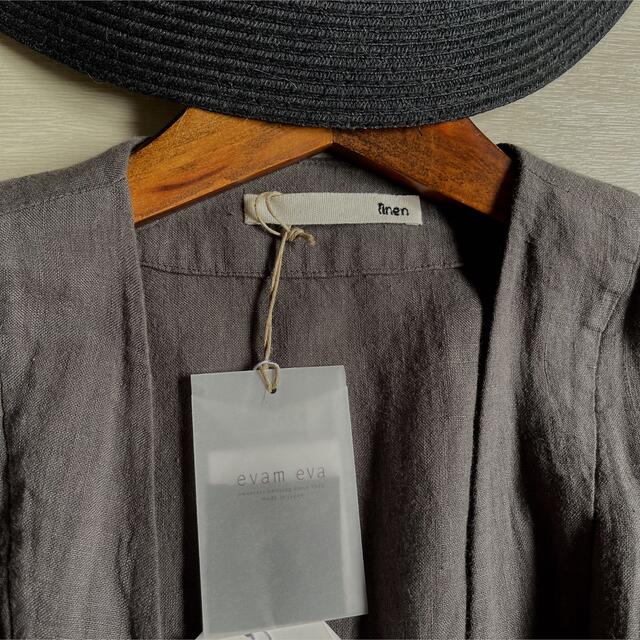
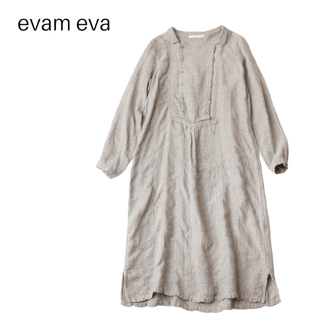
【新品美品】evam eva ネイビー長袖ワンピース
(税込) 送料込み
商品の説明
袖丈···長袖
カラー···ブルー
柄・デザイン···無地
季節感···春、秋
一目惚れで購入しましたが、着る機会がなかなかなく、出品いたします。商品の情報
| カテゴリー | レディース > ワンピース > ロングワンピース |
|---|---|
| 商品のサイズ | FREE SIZE |
| ブランド | エヴァムエヴァ |
| 商品の状態 | 新品、未使用 |

エヴァムエヴァ ワンピースの通販 100点以上 | evam evaのレディースを

evam eva - 【新品】evam eva vie 今季完売 リネンワンピースの通販 by

楽天市場】evam eva エヴァムエヴァ リネンワンピース E233T065

楽天市場】evam eva エヴァムエヴァ リネンワンピース E233T065

evam eva - evam eva 新品| やわらかな 上質 リネンローブ 羽織り

evam eva - evam eva 新品| やわらかな 上質 リネンローブ 羽織り

2023年最新】Yahoo!オークション -evam eva エヴァムエヴァコットン

エヴァムエヴァ ワンピースの通販 100点以上 | evam evaのレディースを

evam eva - evam eva 新品| やわらかな 上質 リネンローブ 羽織り

evam eva - evam eva 新品| やわらかな 上質 リネンローブ 羽織り

2023年最新】エヴァムエヴァ/長袖/ロングワンピースの人気アイテム

エヴァムエヴァ ワンピースの通販 100点以上 | evam evaのレディースを

□【定価3.7万】エヴァムエヴァ evam eva *ファインプリーツワンピース

特価正規店】 evam eva ワンピース Ieybt-m61493290030 actualizate.ar

楽天市場】evam eva エヴァムエヴァ リネンワンピース E233T065

美品 evam eva ワンピース 2022ss 本命ギフト 11172円引き www

楽天市場】evam eva エヴァムエヴァ リネンワンピース E233T065

2023年最新】Yahoo!オークション -evam eva エヴァムエヴァ ワンピの

エヴァムエヴァ ワンピース evam eva コットンリネン ワンピース cotton linen one-piece E231T155 レディース-hana shoes & co.

楽天市場】evam eva エヴァムエヴァ リネンワンピース E233T065

2023年最新】Yahoo!オークション -evam eva エヴァムエヴァ ワンピの
evam eva - evam eva 新品| やわらかな 上質 リネンローブ 羽織り

美品】evam eva エヴァムエヴァ ニット カシミヤ100% Vネック S

2023年最新】Yahoo!オークション -evam eva ワンピースの中古品・新品

evam eva(エヴァム エヴァ) 【2019aw新作】 コットン ウール

evam eva(エヴァム エヴァ) 【2022aw新作】コットン スリーブレス

evam eva - evam eva 新品| やわらかな 上質 リネンローブ 羽織り

2023年最新】Yahoo!オークション -evam eva エヴァムエヴァコットン

evam eva リネンプルオーバー 超歓迎 10098円 www.coopetarrazu.com

2023年最新】Yahoo!オークション -エバムエバ evam eva スカートの中古

クーポン対象外】 プラージュ 美品♪ リネンブレンド 青ストライプ L
エヴァムエヴァ ワンピース | 通販・人気ランキング - 価格.com

2023年最新】Yahoo!オークション -evam eva エヴァムエヴァ ワンピの

グランドセール 【美品】ネストローブ リネンノーカラーブラウス

evam eva プレスウールロングコート YAECA リンネル 【日本製】 www

楽天市場】evam eva エヴァムエヴァ リネンワンピース E233T065
evam eva - evam eva 新品| やわらかな 上質 リネンローブ 羽織り

2023年最新】Yahoo!オークション -evam evaの中古品・新品・未使用品一覧

楽天市場】evam eva エヴァムエヴァ リネンワンピース E233T065
エヴァムエヴァ ワンピースの通販 100点以上 | evam evaのレディースを



商品の情報
メルカリ安心への取り組み
お金は事務局に支払われ、評価後に振り込まれます
出品者
スピード発送
この出品者は平均24時間以内に発送しています















